Router Kali Linux Internet Proxy server Wireshark, linux, computer Network, electronics, text png | PNGWing
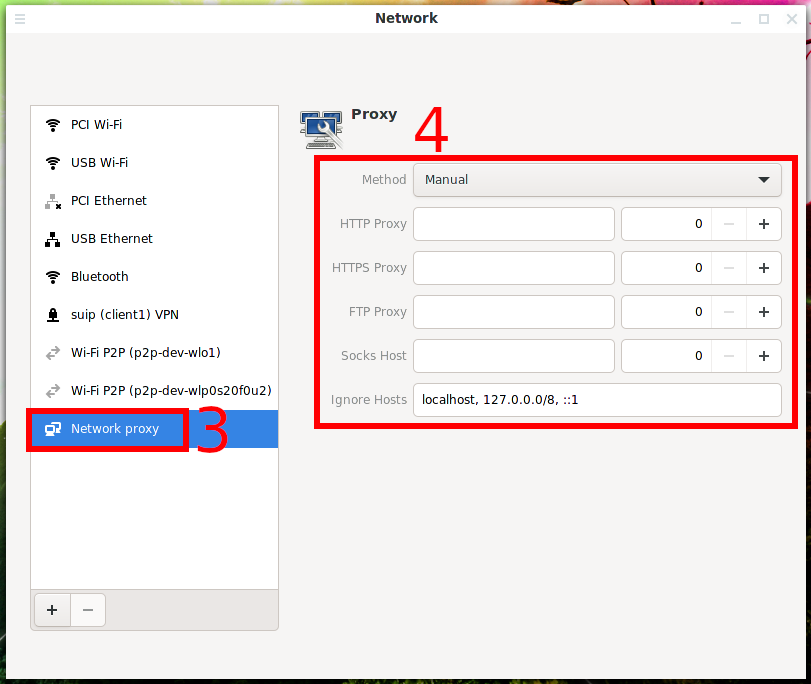
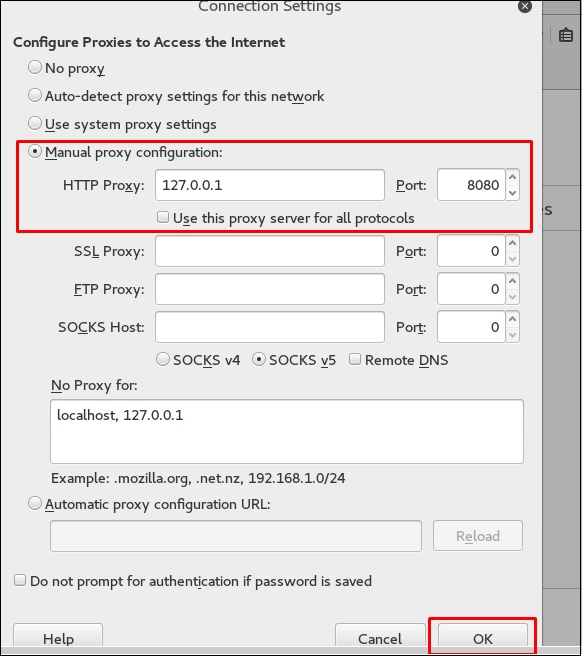
![Adjusting network proxy settings - Mastering Kali Linux for Advanced Penetration Testing - Third Edition [Book] Adjusting network proxy settings - Mastering Kali Linux for Advanced Penetration Testing - Third Edition [Book]](https://www.oreilly.com/api/v2/epubs/9781789340563/files/assets/54634bb5-301a-4657-87ae-7833d4631248.png)
Adjusting network proxy settings - Mastering Kali Linux for Advanced Penetration Testing - Third Edition [Book]

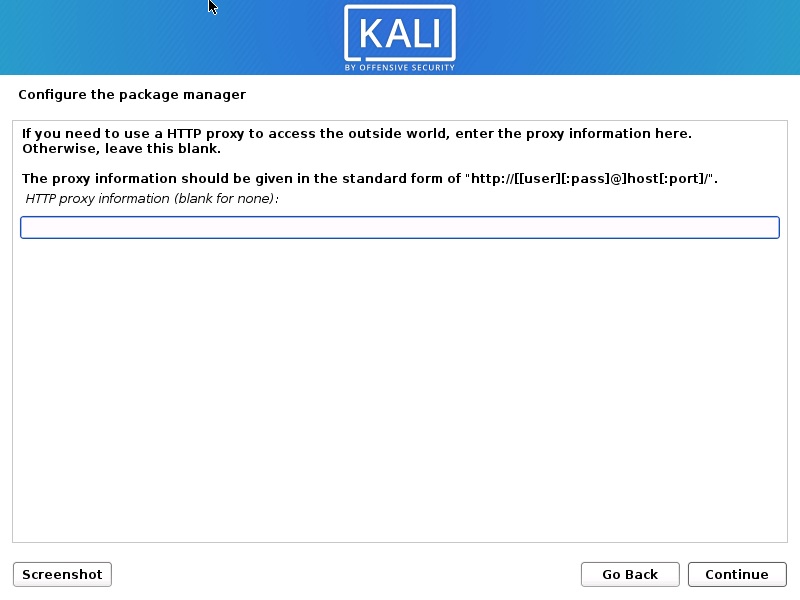
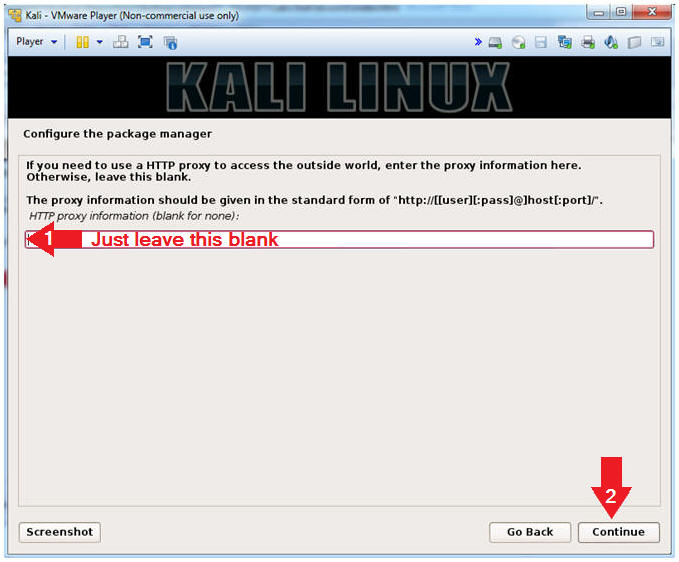
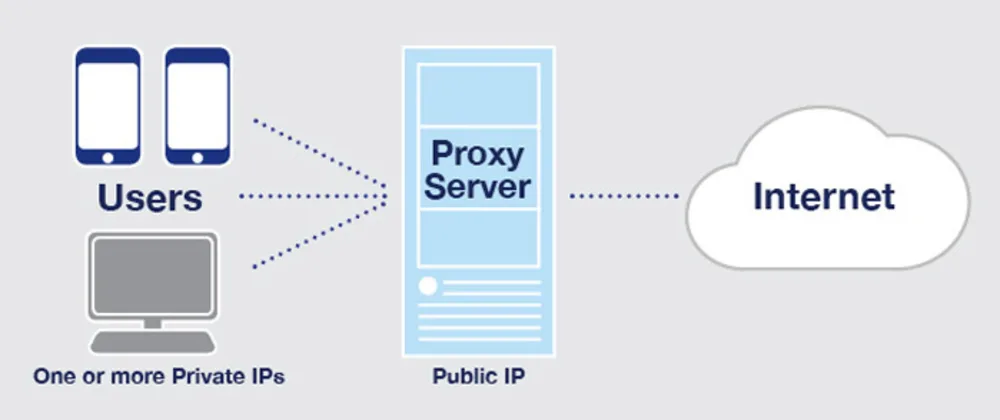
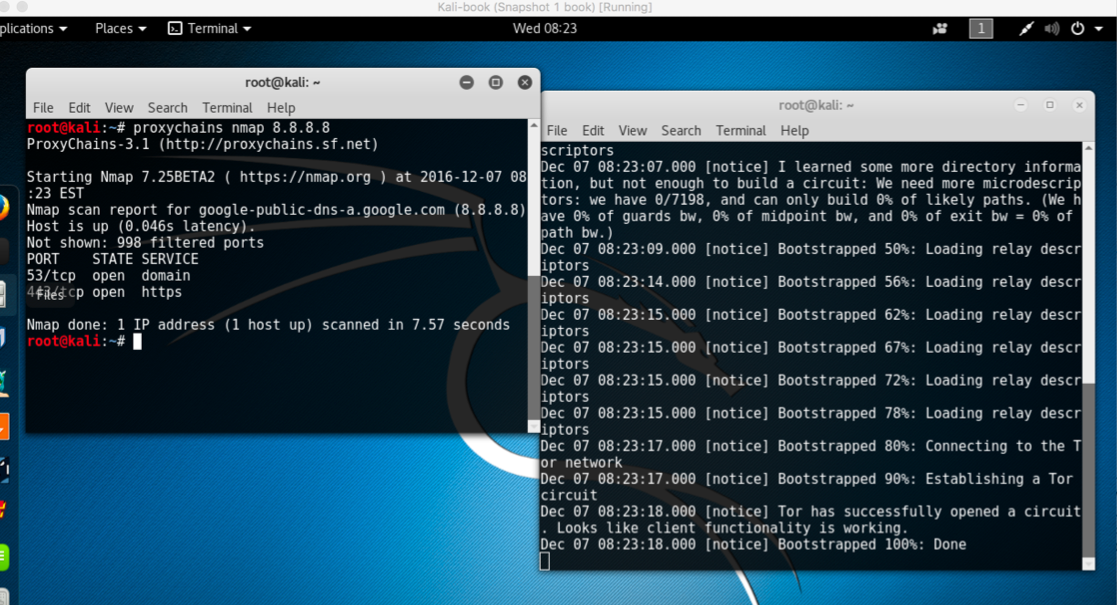
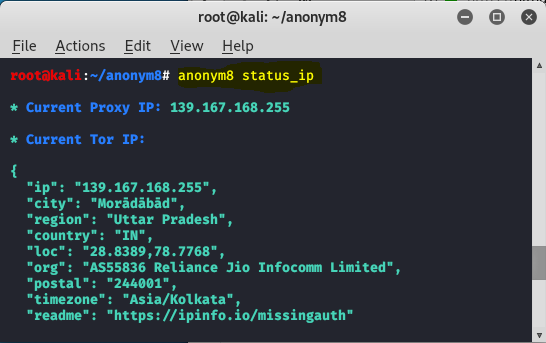
Configuring programs and operating systems to work through a proxy - Ethical hacking and penetration testing

Configuring programs and operating systems to work through a proxy - Ethical hacking and penetration testing